This article explores the transition and meaning of “Democratic Republic” as it was understood at America’s Founding, versus how it is viewed by many in 21st Century America. Without a doubt, there’s a stark contrast between the two eras, and the implications of it are concerning. Read on to learn more.
What is the definition of “The Politics of Having Your Cake and Eating It, Too?” The phrase was first used by former British Prime Minister, Boris Johnson, during the process of extracting Great Britain from the European Union, otherwise known as “Brexit.” Johnson opined, it is the “pursuit of mutually exclusive, incompatible political goals—specifically, trying to secure the benefits of a decision while avoiding its necessary, often negative, costs.” Johnson further stated, “the phenomenon regarding ‘cakeism’ implies keeping advantages while rejecting obligations.”
The Founding Fathers of the United States wrote the Declaration of Independence and the Constitution explicitly to enshrine life, liberty and the pursuit of happiness in perpetuity. Their concept of these principles in life, and in politics, were based on fair, moral and ethical principles.
These principles enable democracy to work based on majority rule, as intended. Democracy and majority rule decays when the enabling principles lose their influence on politics and society. What emerges are two truths that define “The Politics of Having Your Cake and Eating It, Too:”
1.) Majority rules might be the hallmark of democracy, but increasingly, people in the political and societal minority are insisting that they should have a niche carved-out of the majority to still get their way.
2.) A growing number of people in America are embracing a socialist agenda, looking for government at all levels to provide solutions to supposed “problems” they perceive as not being acted on. Conversely, the same socialists want the government to step back on issues meaningful to them, but not the mainstream public.
By definition, neither of these two truths can exist without having your cake and eating it, too; which is incompatible with democratic, majority rule.
A simple way of looking at the “The Politics of Having Your Cake and Eating It, Too” is the old political phrase, “you can please all of the people some of the time, and some of the people all of the time, but you can’t please all of the people all of the time.” American politics in the 21st Century has become a selfish quagmire of pushing to get what you want all of the time, and not care what or if anyone else wants.
Keep in mind the following quote by John Adams; it will be important later in the story.
“We have no government armed with power capable of contending with human passions unbridled by morality and Religion. Avarice, ambition, revenge, or gallantry, would break the strongest cords of our Constitution as a whale goes through a net. Ours is made only for moral and religious people. It is wholly inadequate to the government of any other kind.”
Introduction
This topic requires some historical perspective on America’s original 13 colonies. In modern times, the founding of the United States of America is often thought of as a tight knit group of colonies (states) that equally despised the British Crown and its government. The reality was different.
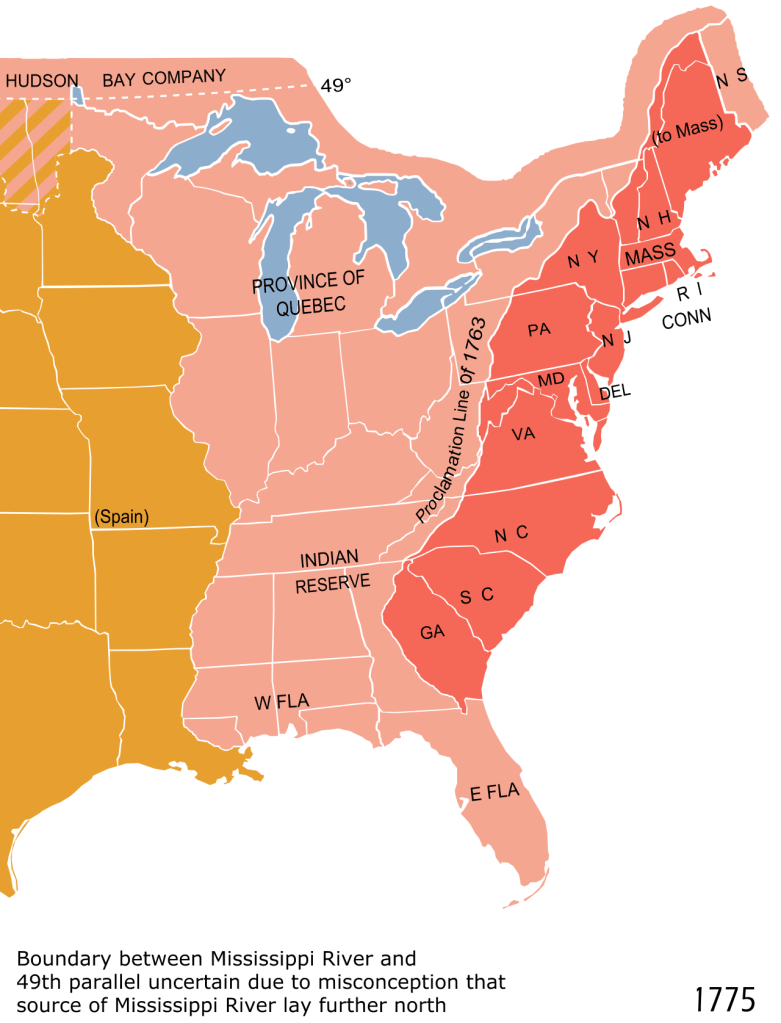
Each colony had its authority and legal right of existence from the King of England in the form of a written charter. To be clear, each colony had its own, separate charter. The charters did not create any legal ties by the Crown between one colony and another. Each one had its own government and elected officials.
There was one exception, however, to elected officials throughout the colonies: Each colonial governor was appointed by the British Government. It was common for governors to reside in England, and then move to America to assume their duties. British Governorships were common practice for all colonies worldwide.
It’s a bit ironic that even though the colonists were officially British citizens, the vast majority had never been to England, often spanning several generations. Colonist allegiance to the Crown was a mixed bag of staunch loyalists, ambivalent citizens (not necessarily disloyal), American independence sympathizers, and staunch supporters of American independence. Aside from the well known Founding Fathers, you could not be sure of someone’s feelings about the War for Independence.
A further twist to the story was that the 13 colonial charters were not issued for the same purposes. For example, the Pilgrim’s charter for Massachusetts was granted for religious autonomy from the Church of England. The Virginia colony established at Jamestown was for commercial purposes to make money for the British Crown.
The colonies were definitely not based on a cookie-cutter model. Some colonies, such as New York, Virginia and Massachusetts, were quite prosperous. In any event, they all did business with each other to one degree or another, and were relatively contented with their lot in life through the 1750s.
During this timeframe the British fought the French & Indian War over the control of Canada, and the unsettled areas around the Great Lakes. The British won the war. Future President, George Washington, was an officer fighting for the British. Other colonists also fought for the British, but mostly as militiamen.

The war was not fought on behalf of the colonies. In general, the colonists who fought in the war, did so as loyal subjects of the Crown. In fact, Washington’s desire was to become a professional officer in the British Army. Promises made to him by British generals were reneged. This left a bad taste in Washington’s mouth; it was a lesson he never forgot.
Although the British won the French & Indian War, the government was left with massive debts. Nothing was said about the war in relation to the colonies, but it soon became apparent in the early 1760s. Under the direction of the King, laws were passed affecting just the American Colonies that began imposing taxes on numerous things.
After making some inquiries, the colonists were told that the taxes were being levied to pay British war debts. Now, all of a sudden, the colonists learned that the Crown was saying the French & Indian War was actually fought on behalf of the 13 colonies, so it was only fair that they should contribute to servicing the debt!
This “taxation without representation” situation referred to the British Parliament passing the tax laws, but was bereft of any membership from the Colonies. It may not have been clear to the colonists in the 1760s, but hindsight by future generations would come to know that the hated taxation was actually the beginning of the end to British Rule in America.
What Happened Next?
Independence was declared on July 4, 1776, and the Founding Fathers dispersed to their Congressional duties during the war. James Madison and a couple of delegates broke-off to start drafting the document that would define the parameters of a new government.
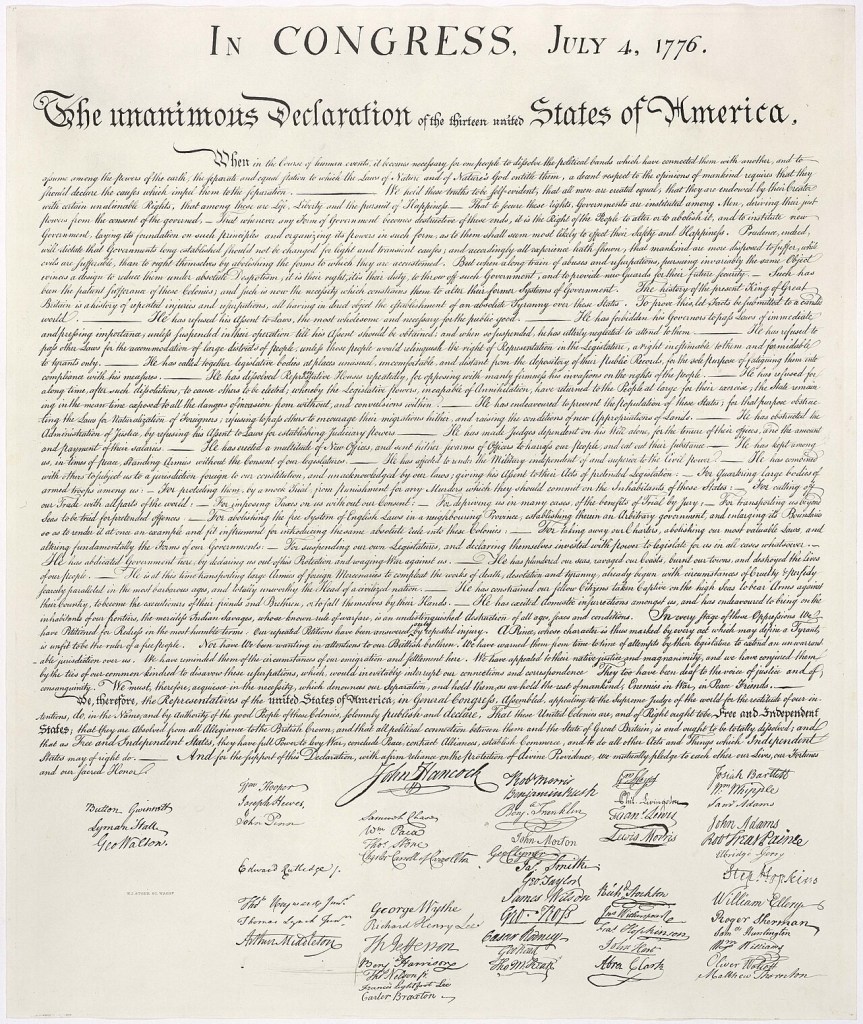
The Founding Fathers who signed the Declaration of Independence were prominent members of society; some were more well-to-do than others. The most common denominators were: significant land holdings and business interests, including: farm owners, bankers, merchants, attorneys, import-export traders, and politicians.
The Founders were also well educated. Many of them were connoisseurs of books with impressive personal libraries. The U.S. had an impressive inventory of books in the Library of Congress; that is until the British Army burned it down in the War of 1812 and lost its entire collection. Upon his death in 1826, Thomas Jefferson bequeathed his whole book collection to Congress. The Jefferson collection was the largest one in the U.S. for its time, and easily surpassed the size of the Congressional Library prior to its burning.
James Madison and other patriots were well-versed in the “Classics” taught in a liberal arts education. This included studying the ancient governments of the Roman Republic, Sparta, and Athens. There were significant writings on politics, ethics, and societies, by famous scholars, including: Socrates, Aristotle, Plato, John Locke and Edmond Burke.
The importance of the Founding Father’s liberal arts education cannot be overstated. The work of standing-up a sovereign country and a new government – a democratic republic – was a serious undertaking. They learned from the Classics that if they did not favor a constitutional monarchy, such as what they were living under as British subjects, with known civil and human rights restrictions, then they needed to know what and how to create something better.
It was not good enough for the colonists to simply dislike the British Government. The Founders understood the need for a new government that was serviceable and avoided the miscues of previously felled ancient democracies like Rome. This would be a tall task because it exposed the significant differences of opinion on state’s rights versus a strong central government. The colonies were not ready to surrender their staunch self rule.
It took Madison several years to complete the first governing document. Their work yielded a document entitled the “Articles of Confederation.” Whereas, the eventual U.S. Constitution was written over the summer of 1787, the Articles of Confederation took several years due to the exigencies of wartime.
A key factor in slowing the writers was the British Army’s vigilance in seeking the arrest of the Declaration of Independence signers; they were considered traitors by the British Crown. If any of them got caught, they would likely be imprisoned for treason. This made out-of-town travel quite precarious, thus impeding the writing of the Articles of Confederation.
The Articles of Confederation were seriously flawed. The scales of politics were heavily weighted toward state’s rights. The postwar need for a strong central government was not yet apparent. The Articles were ratified and took effect in 1781 while the war continued. Within a couple of years, the Articles’s flaws were painfully evident. In 1787, four years after the war ended, the Constitutional Convention was convened in Philadelphia to fix the problems with the Articles of Confederation.
The convention goers pivoted to writing an all new document and scrapped the Articles of Confederation. The new U.S. Constitution was ratified by the states in 1788-1789. Elections were conducted and George Washington took office as the first President of the United States of America in March 1789.
James Madison was elected to Congress and set about fulfilling his promise to write a Bill of Rights as the first 10 amendments to the Constitution. The Bill of Rights ensured the Declaration of Independence’s precepts of the right to life, liberty and the pursuit of happiness, were codified in the Constitution.
Circling Back to John Adams’ Quote
Not withstanding the poor treatment of African-American slaves and Native Americans, none of the colonists needed an explanation of the meaning behind “the right to life, liberty, and pursuit of happiness.” It was understood by everyone that your right to life, liberty and pursuit of happiness could not impinge upon another person’s rights, and vice versa. It was also understood that in a democratic republic, decisions were made based on majority rule.
As John Adams expressed, you cannot properly ensure people’s rights, if they do not believe in religious tolerance, nor for the need of ethical and moral conduct. Throughout America’s 250 years of existence, but especially in the last 60+ years, society has become less and less desirous of upholding the rule of law, honoring democratic rights, or seeing the benefits of organized religion. These acts of selfish behavior came into full bloom at the start of the COVID-19 Pandemic in 2020, and has continued apace ever since.
The Rights and Responsibilities of American Society in the 21st Century
The following chart will start the discussion…
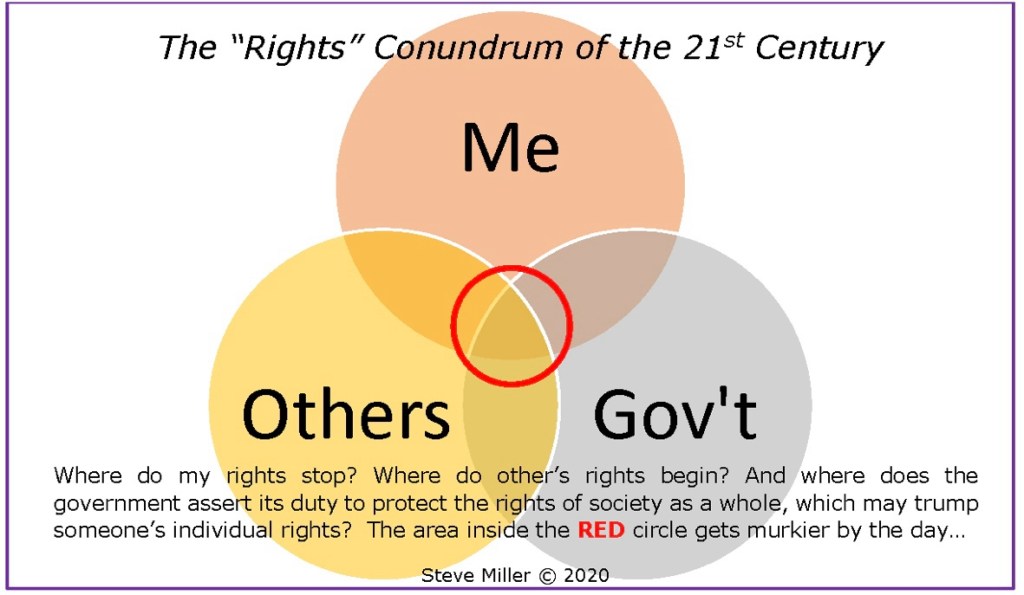
The funny thing about the Rights Conundrum is as the murky red circle expands, each of the three entities begin having less and less respect for the other two, and feel they have to stand-their-ground, not yielding anything, regardless of being right or wrong.
Key factors in this growing lack of respect in America includes: inadequate critical thinking and poor decision making skills. These dysfunctional factors have a strong relationship with an over-reliance on the First Amendment’s “right to free speech.” A common argument by some is the notion that the right to free speech means you should speak-out or act-out on any topic of your choice, anywhere, anytime, and to anyone you choose.
People would do well to speak when spoken to, and be measured in their speech when not asked directly to do so for a valid purpose. First Amendment free speech is a right, not a mandate.
A short phrase that is easily remembered in regards to speaking out-of-turn is: “Opinions offered, but not asked for, are likely to be more important to you, than to the person(s) receiving it.”
How Does This Affect 21st Century America?
Why is unchecked speaking or acting out trending upward, and why is it of concern to the American public? It has a lot to do with wisdom, discernment and judgment. There is an insidious faction in America exploiting the right to free speech. The danger of this is expressed below.
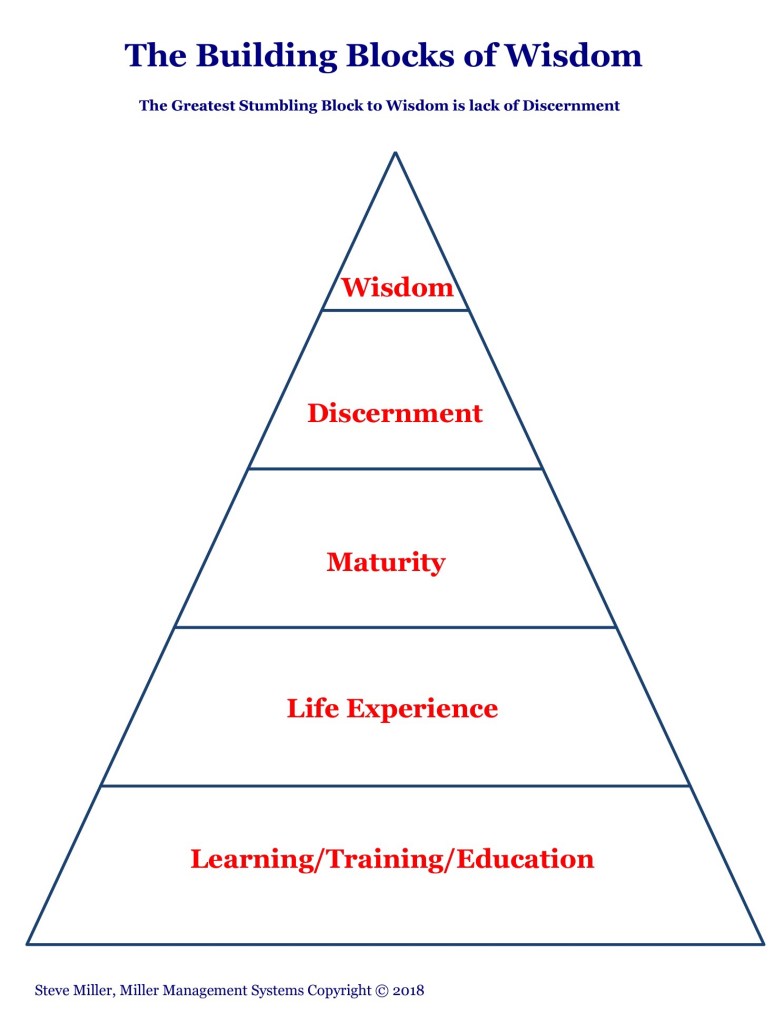
Acquiring wisdom is a building block process; there are no shortcuts. There are people lacking the building blocks, yet will still make decisions based on flawed judgment. And there are people with an education, adequate life experiences and maturity, leading to the top two building blocks. Yet, they erroneously believe they have everything needed to pass judgment, mistaking it for the exercise of wisdom. They would be wrong.
You cannot exercise wisdom if you have not applied an appropriate amount of discernment. Discernment must replace judgment. Discernment has, and judgment lacks, the ability to logically weigh alternatives and distinguish between informed choices.
Judgment makes it too easy to condemn things or people based on flawed information. Chronically poor judgment can lead to profiling, labeling, stereotyping, segregating, and discrimination, which can polarize societies, create anger and divide communities of all sizes. Judgment, rather than discernment, leads to unnecessary extremes that are far apart regarding a central topic.
Judgment without discernment and wisdom, is a necessary precursor to the politics of having your cake and eating it, too.
It is far less likely for someone to press for undemocratic policies and laws if their building blocks of wisdom are fully developed and serviceable.
Serviceability is important because there are people who have fully developed their powers of discernment and wisdom, but will selectively choose not to use them.
The simplest “tell” of someone seeking to have their cake and eat it, too,k in politics is their opposition to an issue supported by the majority, but cannot articulate a reasonable alternative solution.
Let’s Recap for a Moment…
- In discussing the “The Politics of Having Your Cake and Eating It, Too,” it manifests itself in two truths that define the concept. First, political and societal minorities are insisting that a niche be carved-out in-spite of an issue already ruled in favor of a majority. This truth has been successful on several significant issues.
- Secondly, growing political minorities are embracing socialism, looking to the government for solutions to perceived problems they feel are important enough to warrant legislation. Conversely, the same socialists want the government to back down on issues meaningful to them, but not the mainstream public. Examples of this include the nationwide antisemitic protests and the violent immigration enforcement obstruction protests.
- Neither of these two truths can exist under normal circumstances. But, if “The Politics of Having Your Cake and Eating It, Too” is aggressively pursued by the minority, then what seems impossible and incompatible with the democratic majority, may actually come to pass.
- President John Adams pointed out that the U.S. Government was established purposely for a nation of people with moral values and a belief in a power higher than a mere mortal. If someone uses their free agency to reject these principles, the government has little power to do anything about it.
- The Founding Fathers wanted to stand-up a government for their new country that avoided many of the flaws and pitfalls of previously failed nations, as well as, monarchies and dictatorships. They witnessed just how tricky it could be in creating a new government when the Articles of Confederation proved to be problematic. Even when the Constitution was rolled out, it did not include any civil rights provisions.
- Constitutional Convention delegates wrestled with including civil rights, but chose not to, out of concern that it would further delay getting draft copies of the Constitution out to the states. It was expected that ratification could take up to a year to get done. The delegates rationalized that the state constitutions already covered civil rights, so a Bill of Rights for the U.S. Constitution could wait. James Madison observed that each state’s civil rights provisions were different, but he would correct that by the first ten amendments to the Constitution during his first term in Congress.
- The Rights Conundrum noted that the American Government, individuals, and an unknown number of groups, were losing or denying the respect of others, and are disinterested in finding any common ground, unyielding, regardless of being right or wrong.
- First Amendment right-to-free speech is being distorted by the idea that anyone can say anything they want at any time, yet try to deny the right-to-free speech of others.
- Many in the American public are incorrectly passing judgment on a multitude of people and issues, using little or no discernment or wisdom.
Where Does This Toxic Brew Lead Us?
Thomas G. West, PhD, of Hillsdale College wrote an article entitled “The Political Theory of the American Founding.” West discusses the Founders take on Natural Rights, Public Policy, and the Moral Conditions of Freedom. The Founders were greatly concerned about how these issues would play out in a newly formed country and government.
In my July 2020 article entitled, “Defending the U.S. Against Foreign & Domestic Enemies,” I noted, “In simplest terms, our Founding Fathers recognized they were creating a nation with more citizen freedoms than any country on Earth, past or present. Prior to the American Revolution, there had never been a constitutional republic operated solely of the people, by the people, and for the people. All previous efforts to create this sort of nation-state ultimately failed, largely due to internal upheaval. The Founding Fathers recognized the democratic freedoms they hoped to create could be abused & breed internal subversion and violent insurrection.”
“For more than a decade prior to 1776, there were violent and divisive elements at work in the 13 colonies, intent upon keeping the oppressive yoke of the British Crown over everyone. This concern was memorialized and enumerated in the list of grievances noted in the Declaration of Independence. It was the first document of lasting importance to denounce the practice of fomenting domestic enemies, to wit in reference to King George: “He has excited domestic insurrections amongst us…” America’s first leaders had no reason to believe that by simply declaring their independence, enemies bent on fomenting domestic subversion and insurrection would stop such actions.”

The concern about domestic security led Five-star General of the Army, Douglas MacArthur, to say the following:
“I am concerned for the security of our great Nation; not so much because of any treat from without, but because of the insidious forces working from within.”
Prominent figures in American history would tell you the same thing that General MacArthur said. This would include George Washington, John Adams, James Madison, Abraham Lincoln, Theodore Roosevelt, and Woodrow Wilson. In the past 100 years, the likes of Franklin Roosevelt, John Kennedy, Ronald Reagan, and George W. Bush, would all express their concerns about homegrown radicalism, domestic espionage and fomented insurrection.
After the Constitutional Convention in 1787, a discussion ensued between Washington, Adams, Madison, Alexander Hamilton, and John Jay (the soon to be, first Chief Justice of the Supreme Court). The topic of the meeting was what steps could be taken to mitigate the state ratification committees getting bogged down in over analyzing the draft Constitution.
The five men decided the best way to avoid ratification problems was to publish a set of essays that explained the rationale behind various topics in the Constitution. The essays totaled 85, and became known as the Federalist Papers. Alexander Hamilton wrote more than half of them, followed by James Madison and John Jay. To avoid public focus on the authors instead of the paper’s contents, they used a nom de plume, “Publius,” a respected aristocrat and politician who was instrumental in forming the Roman Republic around 509 BC.
The Federalist Papers have been an invaluable resource to scholars and political scientists for over two centuries. The Papers are heavily used by the U.S. Supreme Court as a check on their rulings to mitigate the possibility of drifting away from the Constitution’s original intent. Rather than interpreting the Constitution to mean something different, thereby creating Case Law in lieu of legislation or Constitutional Amendment (such as the Court’s original 1973 Roe v. Wade ruling), the Federalist Papers help the Government to stay within established legal boundaries of making changes. An oversimplified example would be the long standing definition of what a “dog” is, and the Court rules that a dog is now reclassified as a hyena!
Back to the Federalist Papers, and the issues with domestic insurrection and civil unrest. James Madison was the ghost writer of Federalist Number 10, which dealt with “The Union (meaning the Constitutional Republic) as a Safeguard Against Domestic Faction and Insurrection.”
Considering that one of the colonist’s main grievances with the British Government was planting espionage agents throughout the Colonies to stifle the independence movement, there was no reason to believe that disruptive factions would automatically go away and never occur again. Federalist Number 10 explained how the proper use of the Constitution would mitigate factions attempting to use unscrupulous tactics to bend the public will in a direction that was counter to what was legally, morally and ethically acceptable.
An important point in understanding how factions come to be is, whether they are instigated overtly or covertly, they all start with one or two people, and then others are convinced to join them. The originator’s real motive(s) are often disguised.
Numerous safeguards were built into the Constitution to mitigate factions detrimental to the Government and/or the American public. Two of the most important safeguards are: establishing separate branches – Congress, the Presidency and Supreme Court – and the Electoral College scheme for electing the President.
The Electoral College was created in lieu of direct, popular voting. This system prevents a candidate or a zealous, malign faction, from trading “favors” for votes.
An example from back in the day is a candidate’s agent contacting a constituent-farmer to inquire about his family and farm’s general welfare. The farmer tells the agent that his greatest concern was not having enough hay to feed his livestock over the winter. He indicates that his misfortune stemmed from a poor yield of his own crop of hay. The election agent offers to have a wagonload of hay delivered to his barn. Incredulous, the farmer expressed his gratitude and asks how he can return the favor? The agent says he would like to count on the farmer’s vote for the candidate he represents in the coming election? The farmer agrees to cast his ballot as requested.
The second purpose of the Electoral College is to curb the influence of voters in the growing, large urban populations, which would tend to overshadow rural voters. It is unlikely the Constitution will ever be amended to eliminate the Electoral College and replace it with a regular, popular vote system.
It can be seen today in states with large urban population centers. Of the 15 largest U.S. cities, only Ft. Worth, TX and Jacksonville, FL are mostly conservative. At a state level, 14 states typically vote liberal in national elections. The liberal states are located on the West Coast, upper Midwest and the Northeastern states. The inland states are mostly conservative. Eliminating the Electoral College would disenfranchise voters in 70% of the states, in favor of the 14 states with the largest liberal voter blocks.
This is not a liberal vs. conservative issue; it’s just stating the reality of the situation. The non-partisan nature of this situation is evidenced by the fact that when the Constitution was written, there were no political parties, nor a bifurcated voter electorate.
A Word About National Security Implications
The covert espionage campaign waged by the British Crown during colonial times was not a phenomenon of an 18th Century monarchy; it happens worldwide today. Consider the following two statements originating from a foreign country:
“By inserting disinformation in publications, including social media, advocating extremist ideas, inciting racist and xenophobic flashmobs, conducting interstate computer attacks on the critical infrastructure targets that are vital for the functioning of a society, it is possible to “heat-up” the situation in any country, all the way up to the point of fomenting social unrest.”
– Igor Dylevsky, Major General, Deputy Chief of Operations, Russian Military General Staff
And,
“It is necessary to inculcate in the psyche of intelligence agents who conduct clandestine operations, the belief that morals and social norms mean absolutely nothing for intelligence work.”
– The Qualities of an Intelligence Agent, Russian Espionage Training Manual
The foregoing statements are not the exclusive purview of America’s adversaries. The protests during the Covid Pandemic, the Antisemitic Rallies of 2024 or the Anti-Immigration Protests over the past year were not fomented by foreign adversaries; the organizers were American citizens and lawful Permanent Legal Residents.
The real malaise of the “The Politics of Having Your Cake and Eating It, Too” is a perfect tinderbox just looking for a match. This malaise fosters the following things:
- Open disrespect for the majority; #
- Contempt for authority; #
- Name calling that incites violence, causing property damage, unnecessary injury, and sometimes even death;
- Insistence that there may be a majority and a minority, but an individual still wants what they want;
- Making immoral and unethical demands for free speech, yet denying the free speech of others;
- Railing against the Government on one issue, but expect it to support you on other things;
- Shuns accountability when it’s not in their interest.
These seven points of malaise, or problematic behavior, didn’t happen overnight. Prior to the Baby Boomer generation, none of these things were common in America; it changed for the Baby Boomers during the Vietnam War era. The two problems listed at the top with an adjacent # sign, first appeared in the 1960s during the Vietnam War protests. The other five points of malaise are beyond the value system the Baby Boomers grew up with.
Much has changed in all aspects of American life during the timespan from the 1970s through the 2020s. American society, culture, higher education, and Federal Government, have changed so much – including extreme polarization – that these institutions now have environments to support, or at least be indifferent to, the politics of having your cake and eating, too. A key factor in all of this is the corruption of personal behavior. None of the last five points of malaise would have blossomed as they have without the decay of individual morals and ethics.
America will never be perfect, including the government, but it’s the best one amongst the lot of some 200 countries. The good in this country far outweighs the bad. There are two things I always keep in mind about our country and how we go about our daily lives as Americans. I must confess that the following two quotes are not mine, but I wholeheartedly believe in them; they were borrowed from a prominent Christian denomination:
- We believe in being subject to kings, presidents, rulers, and magistrates, in obeying, honoring, and sustaining the law.
- We believe in being honest, true, chaste, benevolent, virtuous, and in doing good to all men; indeed, we may say that we follow the admonition of Paul—We believe all things, we hope all things, we have endured many things, and hope to be able to endure all things. If there is anything virtuous, lovely, or of good report or praiseworthy, we seek after these things.
If we could keep these two thoughts in mind, which align with President Adams admonition, our country and ourselves would be in a much better place. When we, and American institutions, disregard morality and fail to remember our country was founded on the principles of religious tolerance, our personal and collective futures are very much in doubt.
In 2026, is America the same, grand, Democratic Republic of 250 years ago? I am hard pressed to say “yes.”How about you? Maybe America can get past “The Politics of Having Your Cake and Eating It, Too” by focusing less on the individual, or factions of dubious origin, and more on ethics, morality, and the very real dangers expressed by General MacArthur.