Introduction
The catchphrase, “beauty is in the eyes of the beholder,” sets the tone for examining the term, “unreasonable.” What seems as unreasonable to one person (organization), may appear reasonable to someone else, and vice versa.
As of March 11, 2026, the U.S. Navy and Air Force, along with the Israeli Air Force, have flown more than 6,000 strike sorties against 16,000 targets inside Iran’s Islamic Republic, as well as, key maritime targets. With Iran being on the receiving end of Operation EPIC FURY’s bombing campaign, the Islamic Regime’s refusal to capitulate seems unreasonable to the global community.
As duplicitous as the Islamic Regime is known to be, it’s refusal to surrender should not be seen as a patriotic or religious act; it’s merely buying time to concoct a plan of further retaliation. The Islamic Regime cares nothing about being reasonable or unreasonable; neither state enters into their calculus.
America has seen this sort of rigid defiance before by the Japanese and Germans in World War II, and by the Vietnamese Communists in Hanoi during the Vietnam War. All three of these foes were seen by Washington, D.C. leadership as being unreasonable. How America and her allies responded in the face of seemingly unreasonable behavior, varied for each of the three countries. In Germany, as long as Adolf Hitler was in-charge, unconditional surrender was off the table. Even after removal of Japan’s military government leaders, they were still hesitant to surrender unconditionally. The hardliner Hanoi Communists refused to accept any sort of capitulation, and were unreasonable during the Paris Peace Conference. They were forced back to the bargaining table as a result of America’s Christmas Bombing Offensive known as Operation LINEBACKER II. But, Hanoi never surrendered anything.
The Utility of Declaring an Entity Reasonable or Unreasonable
Unless both parties in a dispute have the same or similar value system, determining reasonability is a zero sum game. As long as Party A chooses to label Party B as unreasonable, Party A has three choices: keep doing the same thing, hoping Party B will someday become reasonable, or change tactics to something that resolves the impasse, or reassess whether the situation is even worth pursuing, and walk away if it’s not. A real-life, high stakes unreasonableness situation is worth discussing here as an example.
In my book, “The 99th Strategic Reconnaissance Squadron: The Air Force’s Story of Unmanned Reconnaissance in the Vietnam War,” I covered a situation involving reasonableness vs. unreasonableness in the run-up to the Vietnam War.
In 1961, President John F. Kennedy issued National Security Action Memorandum (NSAM) 55, which directed the Joint Chiefs of Staff to conduct their duties as “more than military men,” by taking-in the geopolitical realities underlying national security issues. NSAM 55 remained actionable throughout the Vietnam War, and was applicable if the three Vietnam Era Presidents (Johnson, Nixon, Ford), wanted to use it. As it turned out, each President did as he pleased, and NSAM 55 remained on the shelf, unused. Although NSAM 55 implied a standard of reasonableness, each President judged it by his own barometer.
Maxwell Taylor, Chairman of the Joint Chiefs of Staff from 1960-1964, was the first senior military officer to put NSAM 55 to the test. He demonstrated good political chops, and easily navigated the halls of power in Washington, D.C., and the Pentagon. Simply put, Taylor fit well with NSAM 55.
On the Eve of the Vietnam War
In early 1964, the National Command Authority (President Johnson, Defense Secretary Robert McNamara, and General Taylor ) were receiving a steady stream of reports from Henry Cabot Lodge, U.S. Ambassador in Saigon, and his military counterpart in-charge of America’s local military assistance command, that the Saigon government and its military forces were struggling under a multitude of self-inflicted problems.
Throughout 1964, U.S. military presence in and around South Vietnam numbered about 25,000 personnel representing the Navy, Army and Air Force. The vast majority of these G.I.s were special operation forces working as advisors to the South Vietnamese military. They were not conducting independent combat operations, but they accompanied their Vietnamese counterparts on offensive missions.
The American military leaders in-country and the Embassy diplomats, all sensed it was only a matter of time before the North Vietnamese and the South’s Viet Cong significantly upped their game.
In response to multiple intelligence reports coming into the National Command Authority from both the State Department and the Pentagon, a new NSAM was issued. This new memorandum directed the Admiral over the Pacific Command to develop a comprehensive list of strike targets in North Vietnam.
There were no hard plans to conduct airstrikes in North Vietnam. The target list was developed for a rainy day. The Joint Chiefs of Staff were directed to evaluate the list, and develop a plan to implement an airstrike campaign, if needed.
When the Joint Staff released the airstrike plan, it fell to the JCS Chairman, Maxwell Taylor, to prepare an executive briefing for the National Command Authority and other key players. The original recommendation was to exhaust every target on the strike list without letting up. To Taylor’s mind, war requires pressing the advantage until the foe either surrenders, or becomes combat ineffective.
Taylor Applies the Tenets of NSAM 55
It was Taylor’s desire to comply with NSAM 55 which led him to soften the tone of his May 1964 JCS recommendation. The JCS’ original wording stated the bombing campaign represented by the 94-Targets List was designed to eliminate (through destruction by bombing) North Vietnam’s physical ability to support the Viet Cong and Pathet Lao in waging an insurgency.
The plan of action was revised to specify one unannounced, surprise attack with a huge ordnance load covering major targets across the country.
Taylor’s rewording sought to look at things from a political standpoint based on the reactions of a “reasonable” man to a major, multi-pronged air attack on his homeland for supporting the destabilizing, political goals, and insurrection of groups in adjacent sovereign countries. The Johnson Administration bought-in to the “reasonable man” theory.
To a certain extent, President Johnson’s own political style of arm-twisting and backing the other guy into a corner, played a role in the Vietnam War policies adopted by the White House. Throughout Johnson’s tenure on Capitol Hill as a Congressman and Senator , he counted on his opponent’s reasonableness when confronted with the opportunity to either acquire something they wanted, or avoid something they did not want.
Western politicians believe that every reasonable man has his price. Johnson, and his colleagues, failed to understand that as far as North Vietnam was concerned, the struggle by the Viet Cong, and Pathet Lao (and the Khmer Rouge later on), put them all in the same boat. These communist-aligned insurgencies, as well as North Vietnam, all viewed the Saigon-based democratic government as being “on-the-wrong-side.”
I have always felt that as long as someone is not a psychopath or sociopath, and has a reasonable level of maturity, it puts them in the largest segment of the global population, or what I call the reasonable and rational majority. Being in the majority has nothing to do with right or wrong, moral or immoral, nor does it mean a group member is always reasonable & rational; we all have our days.
The majority of the population covers a broad spectrum of society, to include prominent people in the 1960s, such as: Dwight Eisenhower, John F. Kennedy, Ho Chi Minh, Nikita Khrushchev, and Fidel Castro. Each of these well-known leaders had many followers, and many detractors. Clearly, what one of these men felt was rational behavior on a given day, might be viewed by one of the others as irrational, or unreasonable.
Robert McNamara and “The Fog of War”
An award-winning 2003 documentary entitled, “The Fog of War,” illustrates a real-life case of political reasonability experienced by Robert McNamara, the Defense Secretary during the Vietnam War. The Fog of War convincingly presents 11 truths he coined about national security, foreign policy & war.
Truth #2 states: “you cannot count on rationality (reasonableness) to save the day.” This is 100% applicable to the frustration with both Hanoi’s and Tehran’s “never say die” behavior in the face of mounting military pressure. To American leadership, both regimes were clearly being irrational & unreasonable. McNamara arrived at his opinion about rationality and reasonableness based on his experience with the 1962 Cuban Missile Crisis; an encounter 30 years later would completely overturn his view.
After resolving the impasse with Moscow about the missiles in Cuba, and tension abated, McNamara and other Kennedy Administration officials thought rational and reasonable behavior had won the day. In 1993 McNamara attended a global symposium where he ran into Fidel Castro. Civility & restraint were maintained by both men as they chatted for a few minutes.
McNamara commented to El Presidente that a near catastrophe was averted in 1962 when cooler heads prevailed. Castro said nuclear annihilation came a lot closer than anyone knew, including McNamara and his cohorts. McNamara’s interest was piqued , and he inquired as to Castro’s meaning. Castro told him that contrary to popular belief, when Washington thought they had nipped things in the bud, there were actually 126 nuclear warheads already on the island! Until that moment in 1993, McNamara & the U.S. Government thought the warheads were still on a ship at sea, and had been turned back as a result of the U.S. Navy’s blockade of Cuba.
McNamara was stunned! He quickly told Castro he had three questions: 1.) Did Castro know the warheads were there the whole time? 2.) What was Castro’s greatest concern throughout the Crisis? 3.) After the Crisis became public knowledge, and negotiations commenced between the White House and the Kremlin, what was Castro’s advice to Khrushchev?
Castro admitted he knew all along the warheads were on the island. His greatest fear was an all-out conventional air, land and sea attack on Cuba by the United States. If this had occurred, his recommendation to Premier Khrushchev was to launch a nuclear attack on America from Cuba.
Castro’s revelation changed McNamara’s mind about a man’s reasonable behavior in the face of adversity. Whereas, Hanoi’s unreasonable behavior was seen by McNamara and others as a one-off anomaly, it was instead, a validation that rational or reasonable behavior is not universally defined.
Johnson, McNamara and General Taylor’s failure to comprehend Hanoi’s brand of reasonableness, led to 58,000 American deaths, and more than a million Vietnamese casualties. The Johnson Administration’s misreading of the conflict’s geopolitics led to the U.S.’ accelerated departure, leaving numerous unresolved issues at War’s end.
Not understanding North Vietnam’s indifference led to the ineffective ROLLING THUNDER bombing campaign, starting in March 1965, and ran for three years. To the Washington establishment, Hanoi’s seeming unreasonable behavior was just one of the manifestations that defied western logic.
The Islamic Republic’s Disinterest in an Unconditional Surrender
The “talking heads” on network news are speaking-out of both sides of their mouths regarding Operation EPIC FURY. On the one hand, Trump started a war when there is supposedly no imminent threat from Iran, which is a ridiculous assertion. On the other hand, the same group of reporters are incredulous that under a massive onslaught of destruction, why does the Islamic Regime allow it to continue and not sue for peace?
There is a simple answer to Iran’s seeming unreasonable indifference to the destruction. Above any other reason for the despotic regime’s behavior, is the survival of the Islamic hardliners controlling the country.
Most people fail to recognize that the Islamic Regime has been planning and preparing for this day for 47 years. The organization pulling the strings of power is not part of the public-facing official government. It’s a shadow government that was created to rigidly control the country at every level of government, and all major civil and commercial institutions, and the largest industry segments, such as, banking, manufacturing, agriculture, transportation, the education sector and the oil industry, to name a few. This ruling, shadow institution is known as The Bayt (pronounced like “bait” used for fishing). The Bayt is designed to survive.
The United Against a Nuclear Iran (UANI) organization
The UANI published a landmark report in February 2026 entitled, “Unmasking the Bayt: Inside the Supreme Leader’s Office, the Hidden Nerve Center of the Islamic Republic.” The report was written by two Iranian-Americans PhDs,, Saeid Golkar, and Kasra Aarabi, the founders of UANI.
Golkar and Aarabi said in their Report about the Bayt, “What has become the most powerful political entity in the Islamic Republic has its roots in Shia Islam’s convention surrounding the Bayt-e Ulema (House of Religious Scholars).” The Bayt is an important part of Shia Islamic doctrine that is centuries old.
In simple terms, senior Shia clerics who have been elevated to ayatollah status (does not necessarily mean they are a supreme leader), and have developed a publicly visible following, are bestowed with the title of “Marja-e-Taqhlid;” this stands for “source of emulation.” Once a cleric becomes a Marja-e-Taqhlid, they are entitled to establish a Bayt. At this point, the Bayt is the nucleus of the cleric’s paid office staff. Bayts commonly employ male members of a cleric’s family. Prior to Iran’s 1979 Revolution, a Bayt office was strictly for religious purposes.
Evolution of the Islamic Republic’s Bayt
In 1979, upon the arrival of the exiled Ayatollah Ruhollah Khomeini in Iran, he was designated as the first supreme leader (until March 8, 2026, there had only been two). Khomeini’s Bayt was with him throughout his exile in France. Due to Khomeini’s unconventional status in exile, his Bayt necessarily assumed quite a few secular duties (i.e.; security, travel & transportation, event planning, etc.), as well as a Bayt’s more traditional religious duties.
When Ayatollah Ruhollah Khomeini died 10 years later in 1989, it was assumed that his son would become the next supreme leader; it never happened. His son, Ahmad, was outmaneuvered by a conspiracy of Hashemi Rafsanjani and the now deceased Ayatollah Ali Khamenei. Khamenei became the supreme leader and Rafsanjani became President. It was Khamenei, with Rafsanjani’s support, who began transforming the Bayt he inherited into a formidable base of political control. The Bayt eventually numbered more than 4,000 staffers and a network of over 40,000 independent operatives.
Shown below is how Khamenei’s Bayt was organized prior to his death a few weeks ago. All functions shown in boldface type are direct members of the Bayt. Although it’s not shown here, each non-Bayt institution has at least one commissar overseer who belongs to the Bayt.
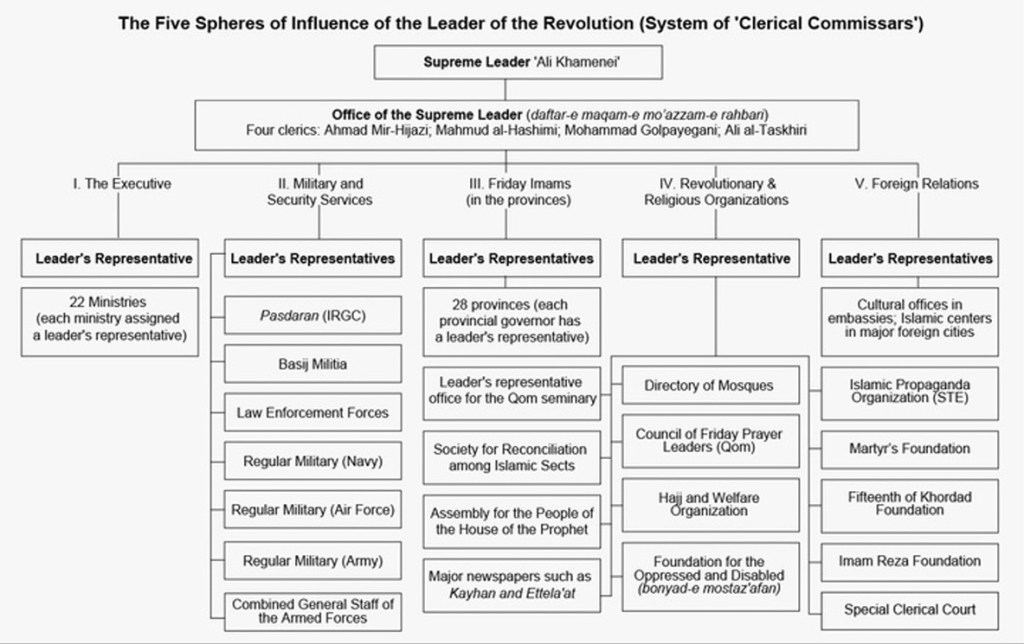
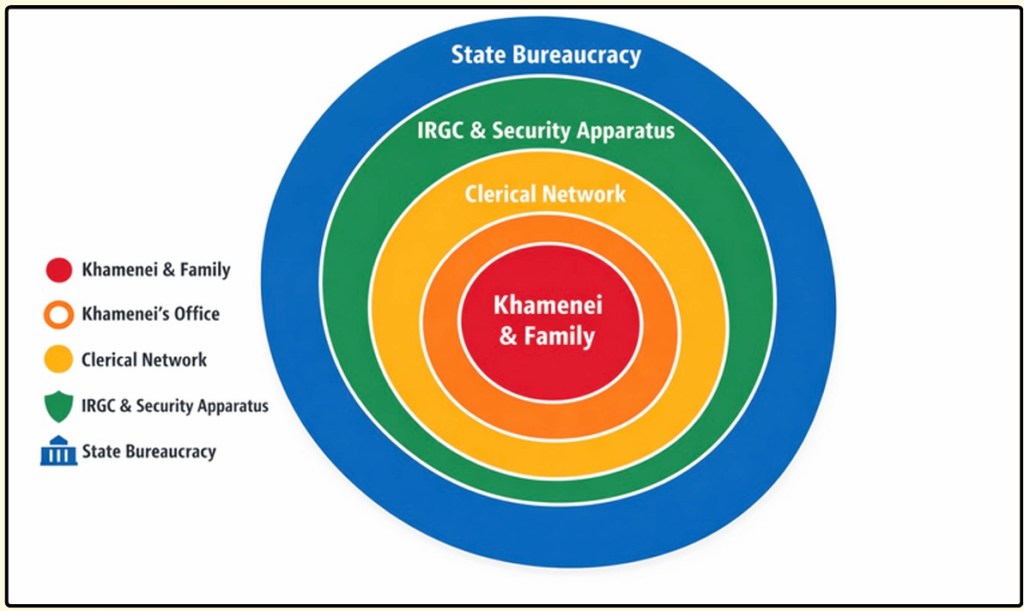
The accompanying graphic depicts how the supreme leader and the Bayt are organized in relation to each other. Other than the outer ring labeled “State Bureaucracy,” which are the public-facing official government agencies, everything else is part of the Bayt, which has no official designation. Since the IRGC functions as an elite military institution, and its headcount fluctuates from new recruits and departing guardsmen, only the officer corps is considered to be members of Bayt.
Khamenei and his hardline Bayt shadow government knew that over the ensuing decades, their infamous agenda would be on every western nation’s radar, especially the United States and Israel. Khamenei’s regime expected Iran would be attacked eventually, and it has.
Expecting an attack in the future, Khamenei’s Bayt began creating a religious, political and paramilitary (IRGC) infrastructure that could withstand a sustained, massive attack. A western military offensive, like Operation Epic Fury, might wipe out the visible signs of public and military infrastructure, but the shadowy Bayt would still be fully functional.
This “next-up-to-bat” dogma can readily be seen after Ali Khamenei’s death on the first day of bombing, including dozens and dozens of other regime officials. Only a week later, the remaining senior Bayt leaders met to vote-in the next supreme leader. The Israeli Mossad’s covert operatives identified the location of the selection conference; it was subsequently bombed, killing all of the attendees. Undaunted by the loss of so many senior leaders for the second time in a week, the remaining Bayt officials met, yet again, in an undisclosed location and chose Khamenei’s son, Mojtaba, as the new supreme leader.
Subsequent to Mojtaba’s ascension, he has not been seen in public. Regime experts have opined about his absence, citing three plausible reasons: 1.) Out of an abundance of caution, his security detail has counseled him to remain in hiding for a while, or 2.) The known injuries he sustained during the attack on his father are serious enough that he is still recovering under a doctor’s care, and; 3.) Announcing Mojtaba’s promotion is a ruse to deflect from the fact that he’s actually dead. This dogged determination by the Bayt to soldier-on as the country crumbles around them, is a good example of unreasonable behavior from a western viewpoint.
Applying the reasonable man theory in the face of relentless bombing, the death of more than 100 senior Bayt and government leaders, and the potential unfolding humanitarian disaster of the civilian populace, the remaining group of Bayt leaders should cease hostilities and sue for peace. But, that would be the actions of a reasonable, rational leadership team; the Bayt is clearly not that.
As long as the Bayt remains in power, regardless of how many senior officials and civilians might become casualties, the Bayt has achieved its ruthless goal of Regime survival. They literally do not care about the death and destruction surrounding them.
What is Next?
Unless the Bayt has a change of heart, rather than retaining its unreasonable position instead, the bombing campaign will not stop. At some point, however, the only way that the U.S. and Israel can achieve their goals is to send in a special forces team to root out the remaining members of the Bayt.
The difficulty of finding and eliminating a high profile adversary can be seen in the Israeli Defense Force’s hunt for Yahya Al-Sinwar, the embedded Hamas commander in the Gaza Strip. As formidable a military force anywhere, it took the IDF two weeks short of a year to locate and eliminate Al-Sinwar. Imagine the effort needed to find senior Bayt leaders in a country that’s twice the size of Alaska! President Trump and Benjamin Netanyahu have some sobering decisions to make if the Bayt leadership remains unreasonable.
Remember: What seems to be unreasonable to America, and her regional Arabic and Israeli allies, is not unreasonable from the Bayt’s viewpoint.
Save this website with an app on your iPhone/iPad or Android phone: While on this website, click on the appropriate button in the upper right hand corner as if you were going to Share the site with someone else. Click on ADD TO HOME SCREEN, and you’re done. On a PC, do the following: Click More Tools > Create Shortcut, and then check “Open as window.”